One of the perks of owning a Pixel phone is that – as well as new Android versions and security patches – you also get a quarterly Pixel Feature Drop, which includes new features and improvements, and June’s drop has got some people extremely excited.
The beta is available now, and that’s led Reddit user schrombear_23 to discover that Google has brought back the vibration mode icon on the status bar, so that you can see at a glance whether your phone is on vibrate.
This is an incredibly small change but also an extremely useful one, since no one wants their phone loudly ringing at an inopportune moment, and with this you can instantly be sure that your handset will only vibrate. It’s a feature that the Pixel line used to have, but which for some reason was removed a while ago.
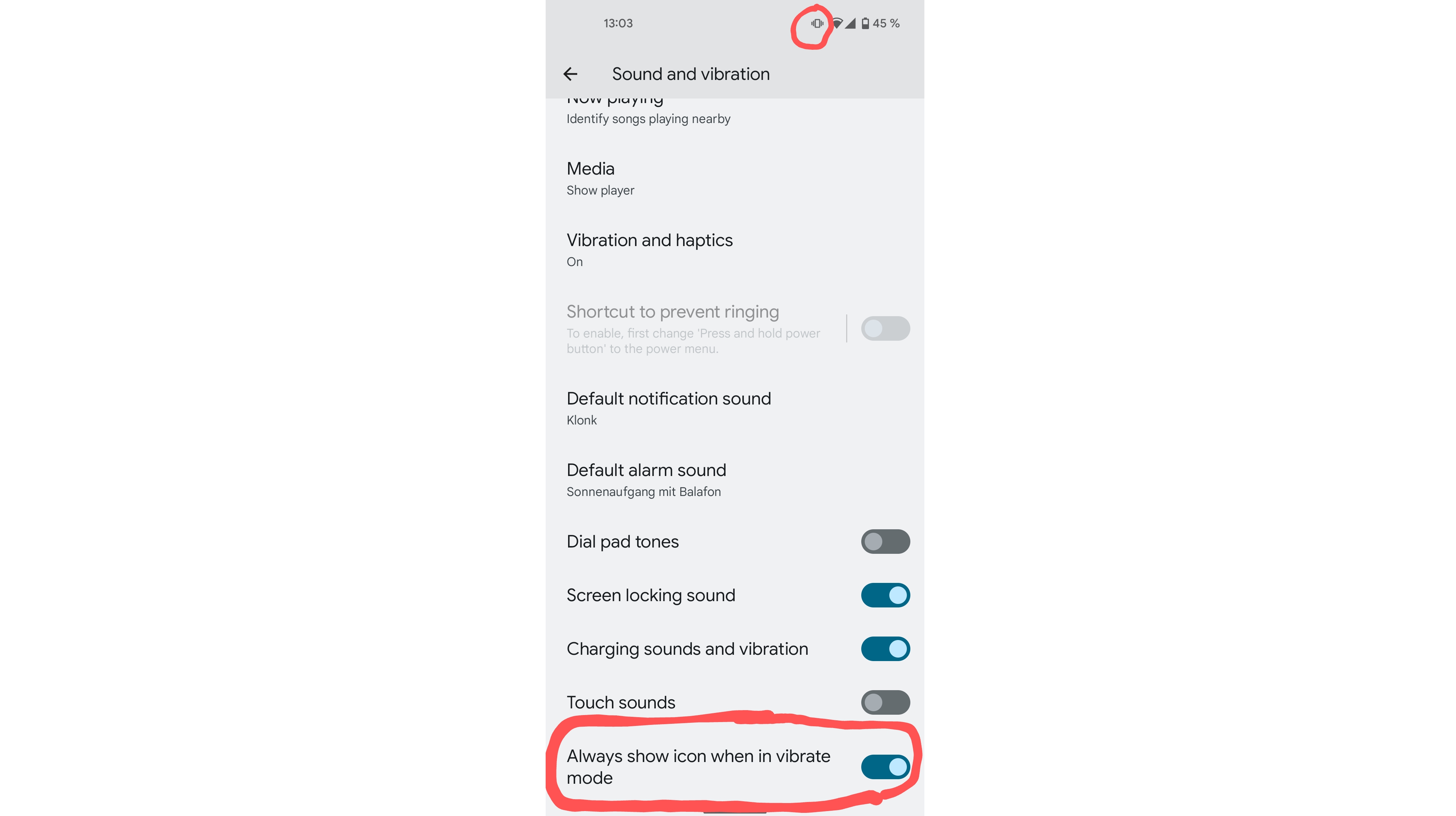
But Google has gone slightly beyond just adding the icon. It’s also added a toggle to the sound and vibration settings screen, which lets you hide the vibrate icon if for whatever reason you prefer not to see it (perhaps you don’t like a cluttered status bar).
Oddly the vibrate icon doesn’t appear on the lock screen status bar, which seems like a weird omission, but since this is just a beta of the software there’s a high chance that the finished version – landing on June 6 – will resolve that.
Just note that this feature is only going to be available for the Pixel 4 and above, so if you’re rocking an older Pixel handset you’re out of luck.
Analysis: a worthwhile feature but one that’s worth waiting a bit longer for
Having a vibration icon on the status bar seems obvious and useful, and it’s baffling that it was ever removed, so it’s great to see this returning to the Pixel line. But while you can grab the beta software with this feature now, we wouldn’t.
Beta software is often buggy and could cause problems with your phone – not just in terms of the new features, but also in areas that were previously working fine.
This could be all the truer on the Google Pixel 6 line, given the problems these phones have had with bugs (most of which have thankfully been resolved now).
The software is due to be released in finished form on June 6, so there’s only a month to wait at the time of writing anyway. Until then we’d suggest you just continue being vigilant about whether your phone is actually on vibrate.
- Get more out of your Pixel with some of the best free Android apps
Via Phone Arena
Source: TechRadar