It's time to practice safe texting.
If you use Google's stock Messages app to send your text and SMS messages, we have good news — your chats can now be completely secured from prying eyes! We'll show you how to enable end-to-end encryption in the Google Messages app so that you don't have to worry about your private messages potentially falling into the wrong hands.
How to enable and use end-to-end encryption in the Google Messages app
End-to-end encryption for Google Messages only works if both the sender and the receiver have it. So if you would like to send an encrypted text to someone, make sure they have it on their phone too.
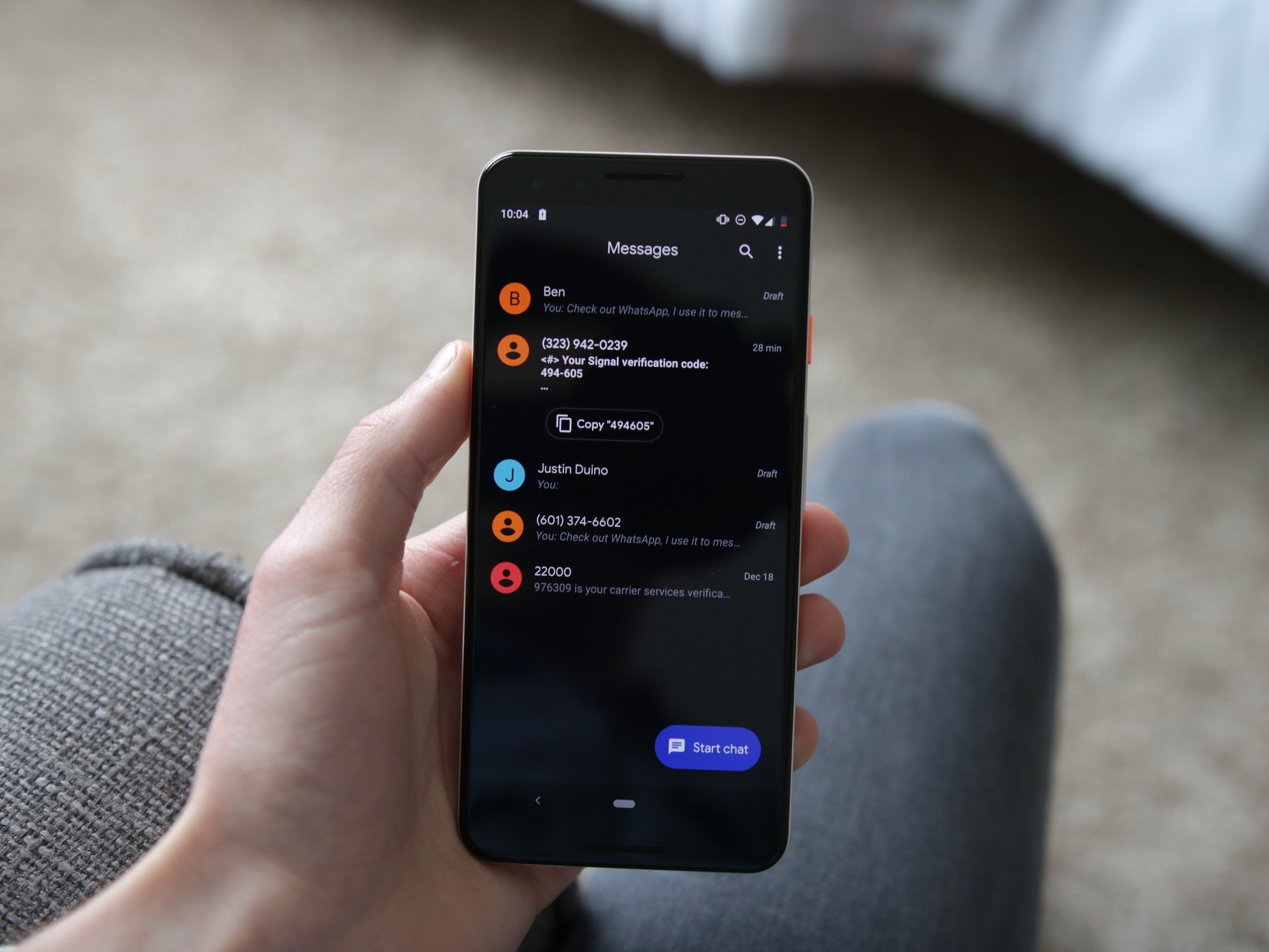
- Open Google Messages.
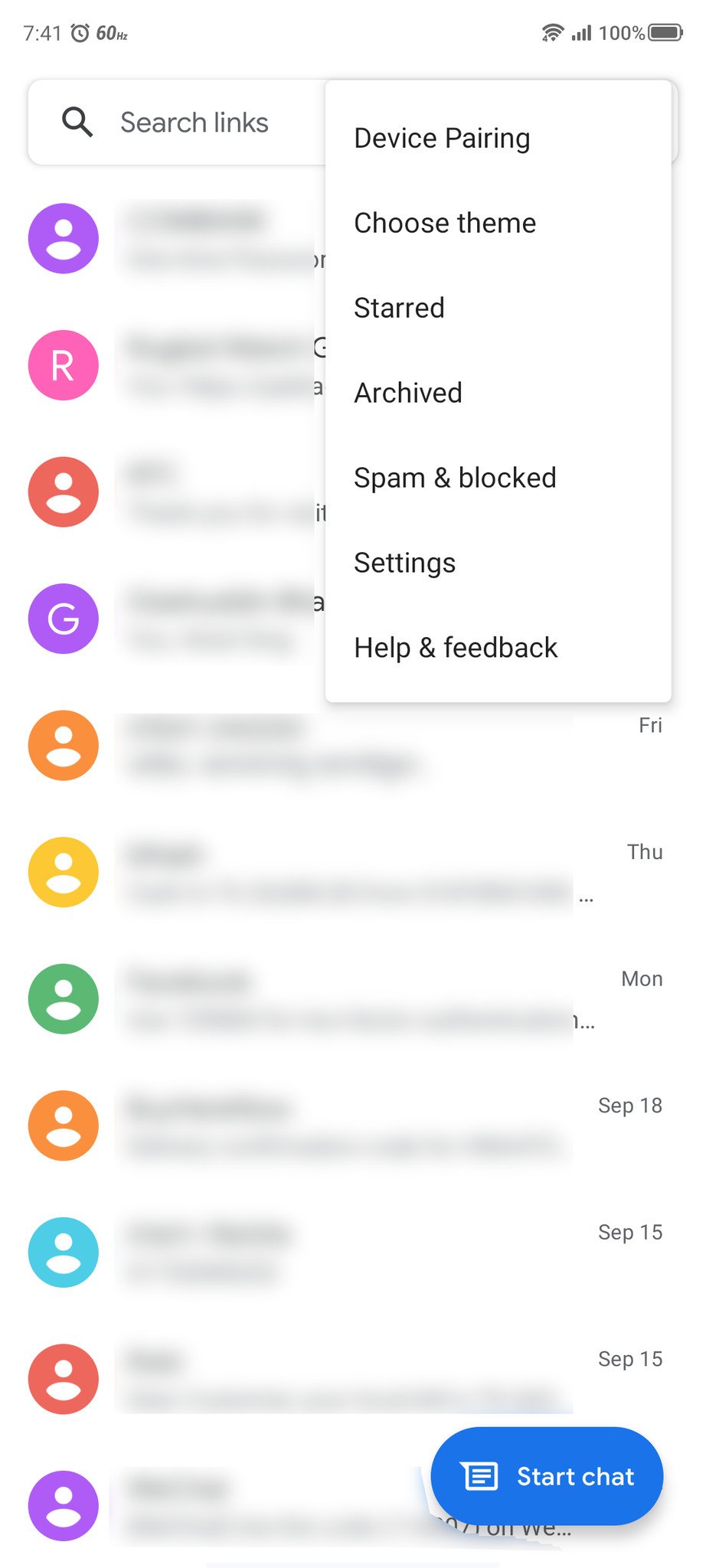
- Tap the three dots in the upper right corner.
- Tap on Settings.
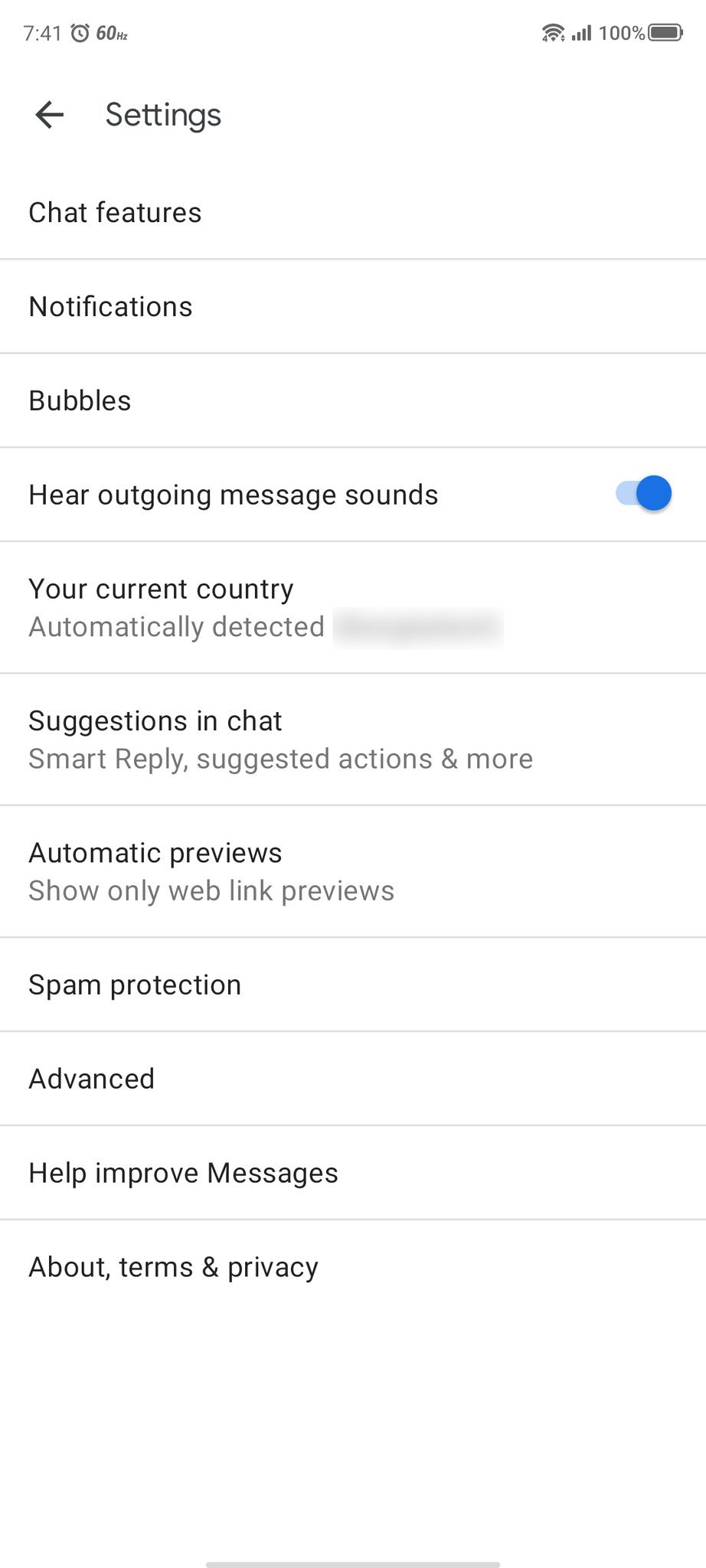
- Tap on Chat features.
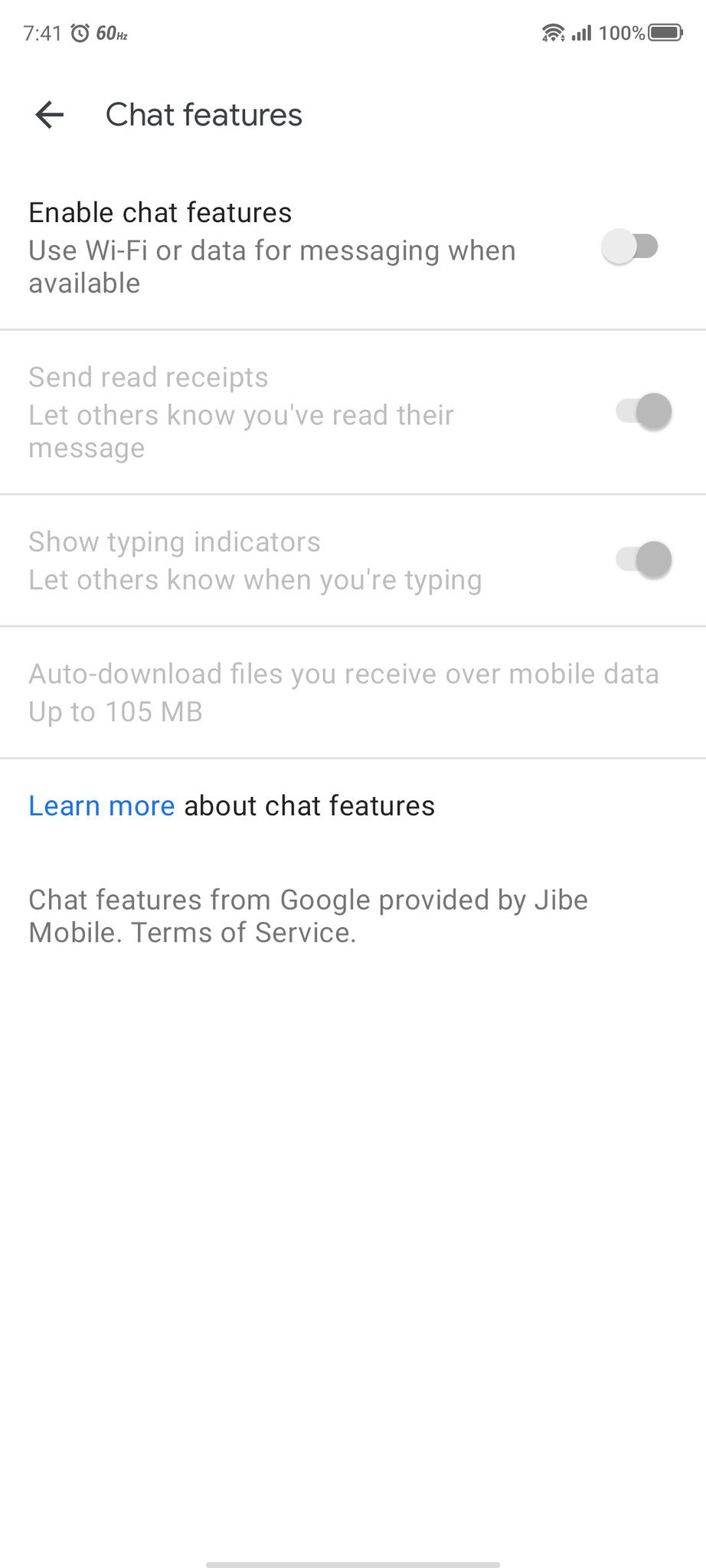
-
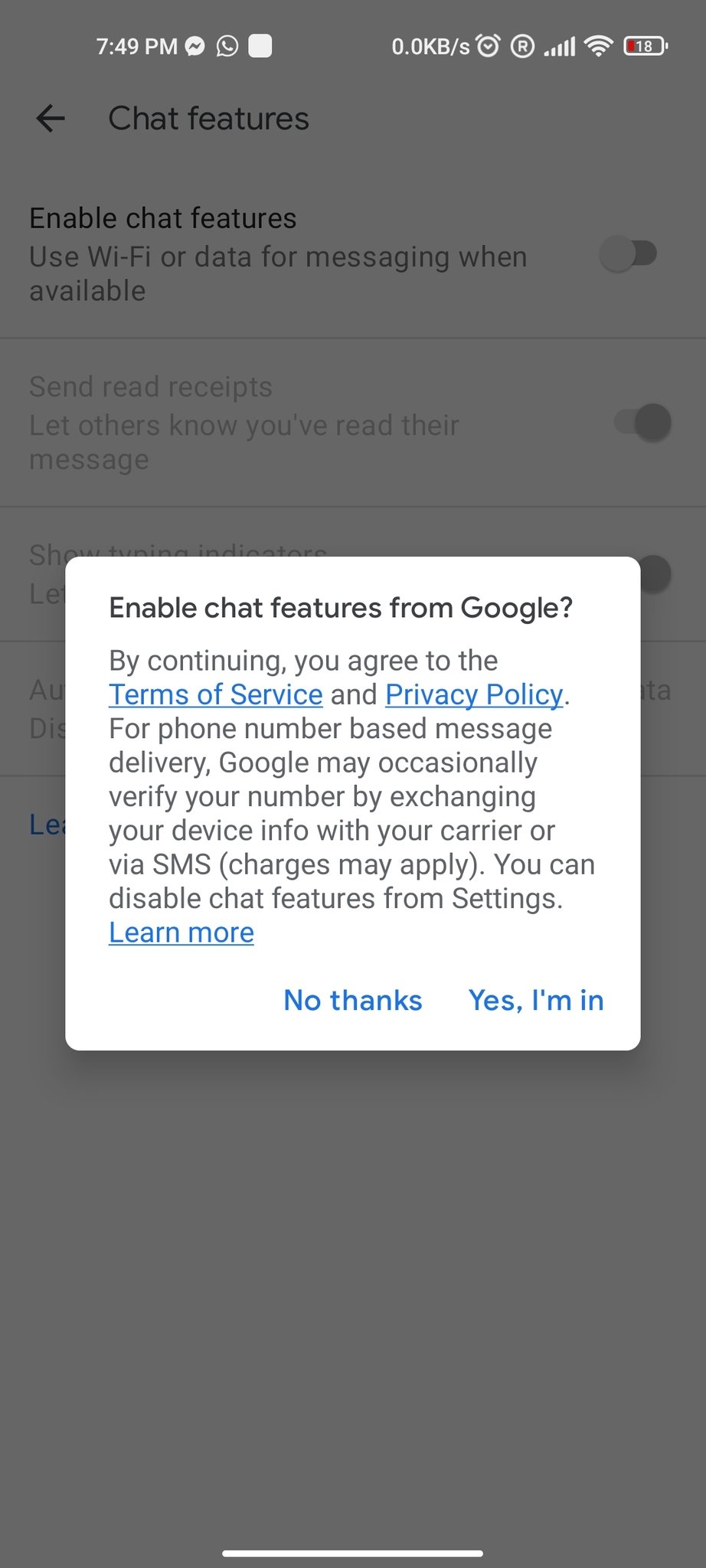
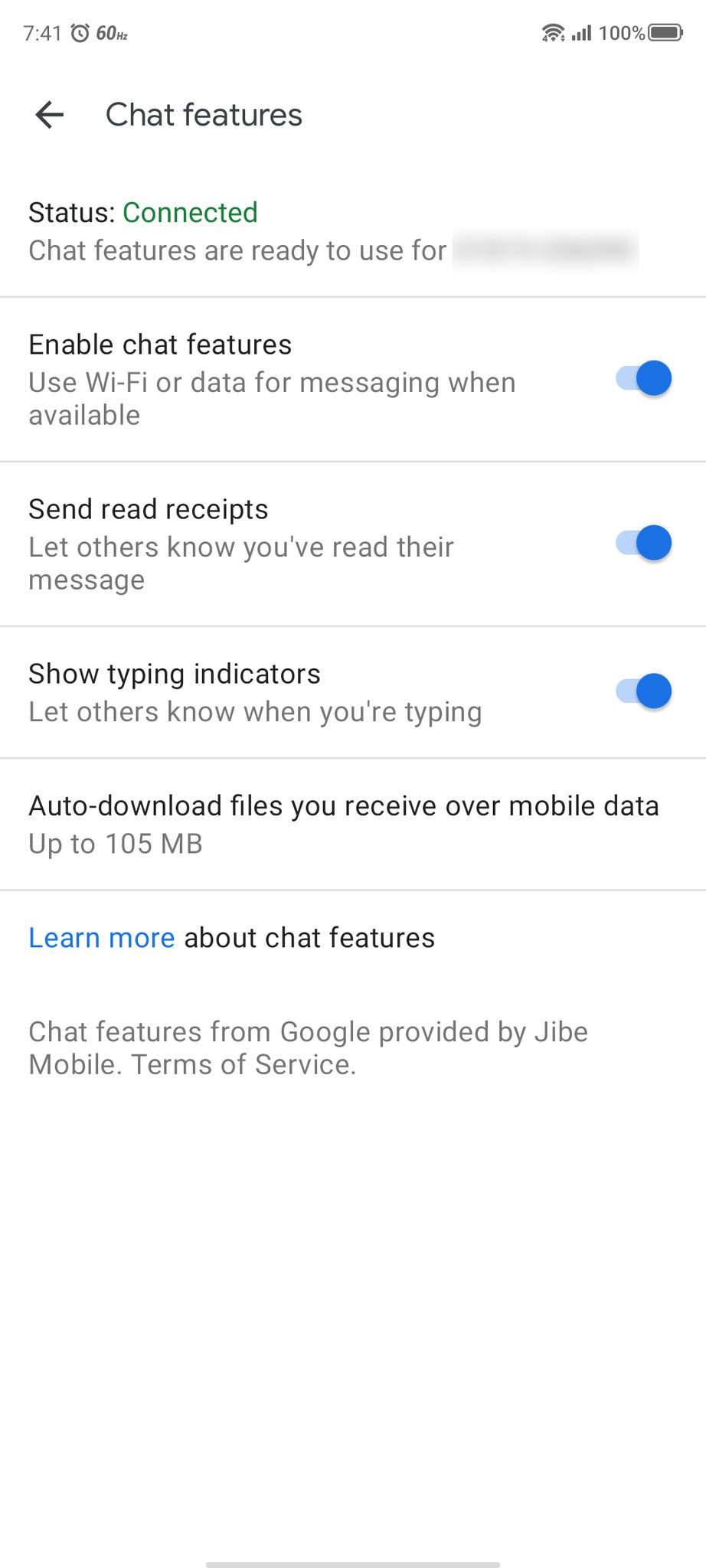
Turn on the toggle for Enable chat features.
- A prompt will pop up asking Enable chat features from Google?, tap Yes, I'm in.
-
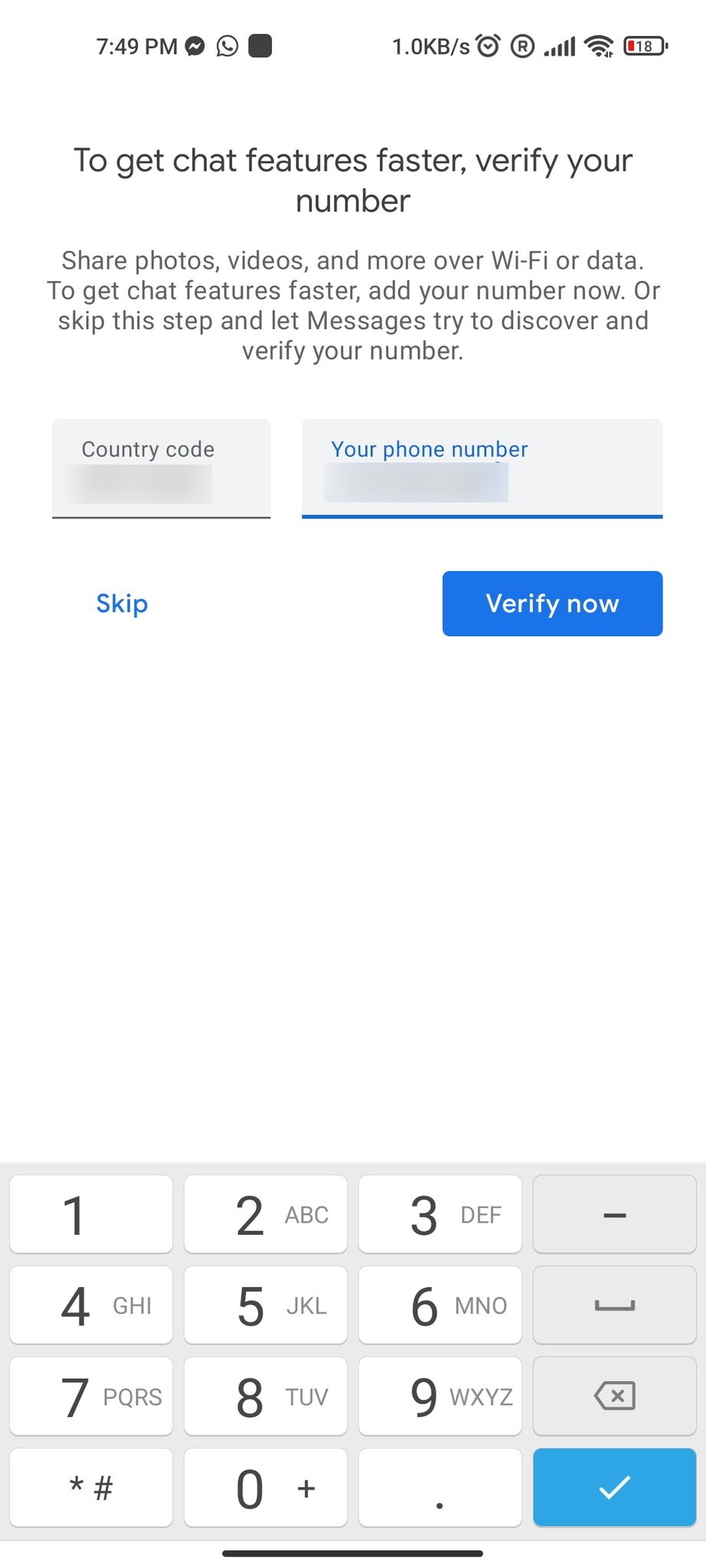
Verify your number.
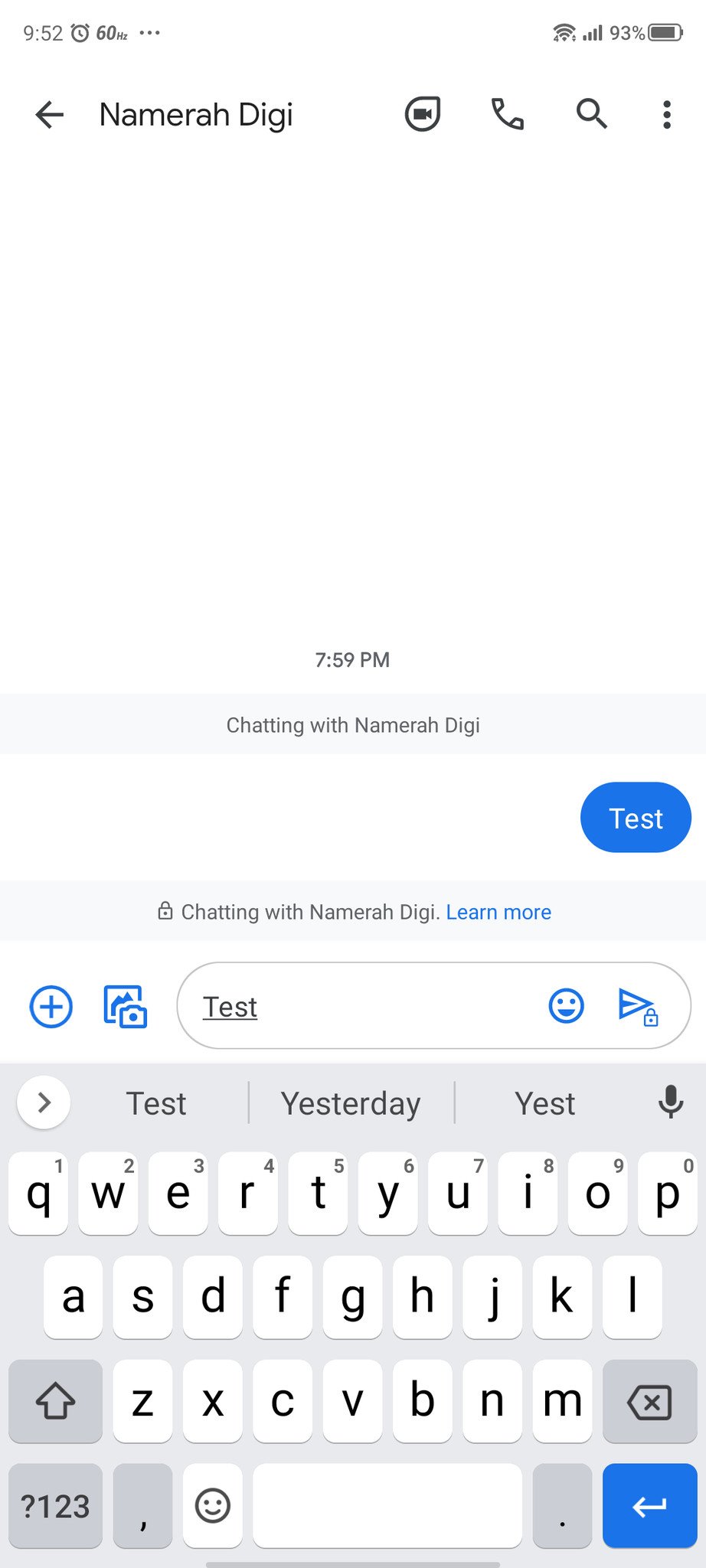
- Open an existing chat or start a new one.
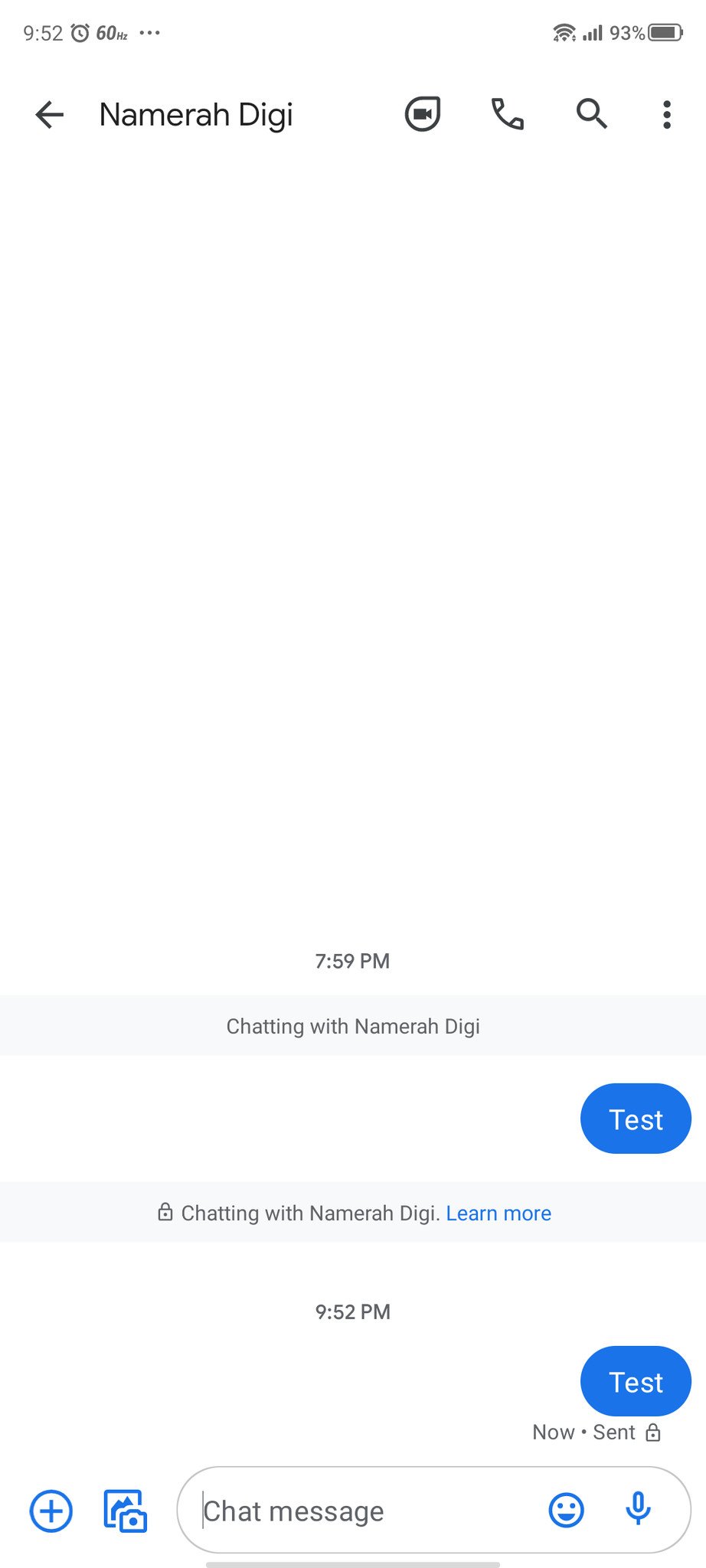
- You should see a lock icon above the message bubble. Tap on Learn more to read about the feature.
-
Send a message to your contact who is also using Google Messages with chat features enables.
- You should see a lock icon after the Sent or Delivered notification, below the chat bubble.
As mentioned before, this end-to-end encryption will only work for messages where both the sender and receiver are using the latest version of the Google Messages app with chat features enabled. This is similar to the way that iMessage works for iPhone users, in that if an iPhone user sends a message to an Android user, the message is not encrypted.
While this is certainly a welcome feature for Google Message users, many of the best messaging apps on Android and iOS also use end-to-end encryption, so you may want to use one of these like Signal, Telegram, or WhatsApp to ensure cross-platform encryption.
Our top equipment picks
All of the best Android phones running the latest OS release are secure, but if you want the most timely security updates and ongoing feature support, you're going to want a Google Pixel device. One of the best and most affordable is the Pixel 4a.
Secure software
Google Pixel 4a
$349 at Amazon $300 at Best Buy
Protection for all
The Google Pixel 4a packs great software with a great camera for less than most mid-rangers or flagships. It is also promised to receive monthly security updates until 2023 at least.
Lock it down
Google Messages
Google's official messaging app supports SMS, MMS, and RCS and now supports end-to-end encryption between users.
Source: androidcentral